Peter Atherton04.05.06
Counterfeiting and Corruption in the Supply Chain
RFID Technology Is Helping to Ensure the Security of Today’s Devices
Peter Atherton
MIKOH Corp.
As processes for moving products and inventory through the supply chain become more automated, increasingly less human intervention is necessary to ensure items make their way from the manufacturer to the surgeon or consumer. While supply chain technology offers increased speed, efficiency and accuracy, precautions must be taken to make up for the lack of human touch along the way. Particularly in sensitive industries such as medical devices—where serious health risks reside—it is imperative that all parties are assured nothing has been tampered with as items travel along the supply chain to the end-user.
In recent years, thieves and criminals have become more sophisticated and have developed intricate plans for taking advantage of weak security in the supply chain—many times involving very few people and no interaction at all with employees transporting the materials. An example of vulnerability in the movement of products from creation to end user is pharmaceutical counterfeiting. According to a 2005 report by Business Insights, the counterfeiting of pharmaceutical products is a multi-billion dollar industry that was previously limited to developing countries, but in recent years has also thrived in nations such as the United States and in the European Union.
Besides the obvious health risk to unknowing users of fake drugs or knock-off medical equipment, the harmful effects of supply chain attacks reach well beyond the hands in which tampered products end up. Manufacturing companies are legally liable for damage caused by their products, meaning their responsibility for the integrity of their products does not end when the items leave the plant door.
Court costs, large settlements and imposed fines are only the tip of the iceberg when it comes to high-profile cases that are splashed across the headlines. The damaging effect a counterfeiting or tampering incident can have on a company’s reputation (remember Tylenol?) can be irreparable, severely impacting a company’s value.
Along with reputational injury and damage control costs, as cases of supply chain tampering are discovered, the direct commercial losses experienced by the businesses involved can become substantial. Even if a case of theft or tampering is discovered early enough to avoid any health risks, the bottom line takes a direct hit due to lost inventory, productivity and profits.
How Do Counterfeiters Do It?
Since the introduction of the supply chain, criminals have been taking advantage of the susceptibility that comes inherently with this system. The very nature of products moving across multiple locations over long distances and under the responsibility of various corporations leaves plenty of room for vulnerability. As the means for tracking items has evolved from manual inventory to barcodes and, finally, to next-generation technologies such as radio frequency identification (RFID), the way in which criminals operate has greatly changed from the days when hijacking trucking fleets was the quickest way to penetrate a system. Now, criminals have found sophisticated ways to interfere with modern technology.
Criminals have come a long way from holding drivers at gunpoint and making off with the goods. Today’s modern bandits have developed ways to infiltrate the supply chain at its weakest points, with minimal disruption to normal activity. It can be as simple as gaining access to the supply and replacing contents of containers with counterfeit or inferior equipment. Because the items and packages are tracked electronically, the heist may not be discovered until the items wind up in consumers’ or users’ hands—making a hasty getaway unnecessary. The thieves could unload the hot items before anyone is even aware the shipment was tampered.
What Are We Doing About It?
Starting in the early 1970s, when the UPC symbol was adopted as the industry standard, barcodes have been used to identify and log products. While barcodes supply us with efficient product identification and inventory control, they provide no physical security for the items on which they are printed. It is still necessary that items be inventoried and shipments manually inspected for tampering and theft along the supply chain.
Recognizing the risk of illegal activity, and in response to the increase in counterfeit drug investigations, in 2004 the FDA created a proactive task force to combat the increasing threat in the United States. This task force has requested that the pharmaceutical industry begin using a more recent technology: Radio Frequency Identification, or RFID.
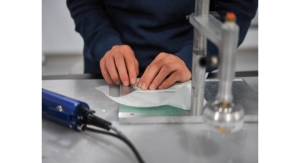
Shipments of medical devices can be traced and monitored using a Radio Frequency Identification tag. Photo courtesy of MIKOH Corp. |
As RFID is adopted by medical device manufacturers to track and secure products through the supply chain, the tags typically take on the form of a self adhesive label with the chip and antenna integrated. These labels can then be adhered to individual items or to seal containers containing multiple products. Items can be tracked as they make their way to their final destination, and tag readers are instantly notified if a tag/item somehow strays from the designated route.
According to FDA Consumer magazine, the FDA is optimistic that the significant progress in the development and implementation of a standard electronic track and trace system using RFID will continue at a rapid pace and will achieve widespread use in the supply chain.
While RFID has shown tremendous potential in improving efficiency and cost in the supply chain and the technology is being touted as the biggest tracking development since the barcode, some important issues still must be addressed, as they have been overshadowed by the amazing benefits promised by providers of the new technology.
The Problem With RFID
This technology provides great speed and efficiency when fully automated; however, conventional RFID labels are not physically secure. With privacy issues “top of mind” as this technology evolves, the physical security of RFID tags has been overlooked. Counterfeiting and theft can still occur with RFID systems in place.
These conventional “sticker-like” RFID tags can easily be moved from one item to another without the tag’s RFID function being affected and, therefore, without the system being aware of the tampering.
Counterfeiters only need to take a few extra steps—removing the RFID tags that seal the containers; taking out the original contents and replacing it with counterfeit items; and then replacing the original RFID tag and sending it back through the medical supply chain as if nothing had happened. Tag readers will continue to track the original tags, even though the contents of the packages have been replaced or the tag has been affixed to a completely different item.
The more common method is to manufacture an entire fake product—packaging and all—and substitute genuine product with fake. The RFID tag can be switched from the genuine to the fake product, and the system will not be aware anything has occurred. The genuine product can then be sold on the black market.
As advances in this technology lead to large-scale applications, physical security is critical to the deployment of this technology. To derive maximum value from an automated system, RFID tags must include a tamper-detection feature that is linked to the RFID function. Otherwise, a system will be monitoring tags only, without any assurance that the tags are still attached to their original items. When a reader reads the RFID tag, that is all it is doing—reading the tag. How can we be assured that the RFID tag is applied to the correct item at all times?
A new kind of RFID tag has been created to detect tampering or removal of the tag and monitor the physical integrity of the package and product. MIKOH Corporation developed a patented tamper-evident technology that is currently being integrated into some RFID labels, adding an extra “tamper-sensing layer” to the tag that causes the antenna to separate from the label and disrupt the performance, ultimately disabling the tag if tampered with. This technology triggers the reader to let people know that something is happening, precisely isolating the point of the event.
Having a physically secure RFID tag protects businesses and users from security compromises and commercial loss through counterfeiting, substitution, theft and other types of fraud. Tamper detection for RFID tags will benefit any application where the integrity of the tag or seal is essential, particularly medical device tagging, container security, document authenticity and monitoring of safety equipment.
It is inarguable that RFID will eventually make the often-predicted tremendous impact on the business world as we know it, but many issues still must be resolved, such as the cost of the tags and concerns regarding privacy. As these systems are being implemented and improved in companies globally, it is also critical to address the physical integrity of RFID tags to ensure the security of their corresponding items as they are shipped to their various destinations.
Industries involving highly regulated and sensitive business practices, such as in the medical field, will likely be the first to adopt technologies that restore confidence in the integrity of their products and equipment. In a high-value industry that relies on the trust and loyalty users feel toward its products, it is critical that extra steps be taken to secure the credibility that comes with a well-protected brand.