Mark Coderre, National Security Practice Director, Chief Information Security Officer, OpenSky Corporation06.02.16
Technology’s transformative power in healthcare has become apparent as physicians access X-ray images and test results from their home computers and administer medications using iPad wireless control devices. Patient care has been improved dramatically by the growth of networking technology employed to transport data throughout healthcare facilities and even to patients located outside the facility.
The other side of the coin, however, is that these networks are more susceptible to hacking to gain access to the main hospital network, steal sensitive patient information, and, possibly, cause devices to malfunction, leading to patient harm. Hackers often exploit vulnerabilities within a medical device software or security loopholes within the wider network to access and steal medical records. From August 2009 to December 2013, 804 major breaches occurred at healthcare delivery organizations (HDO), with “major” defined as more than 500 patient records. (United States Department of Health and Human Services.)
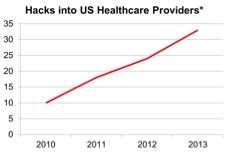
(Source: www.privacyrights.org) *Publicly known
Inadequately secured mobile devices present another gateway for cyber-attacks. Tablets and smartphones are increasingly deployed in healthcare settings to control medical devices, not to mention various gadgets that visitors bring in for personal use.
The issue has figured prominently in the minds of the public and all industry players. In October 2014, the U.S. Department of Homeland Security (DHS) announced it is investigating about two dozen cases of suspected cybersecurity flaws in medical devices and hospital equipment that officials fear could be exploited by hackers.
The DHS’s Industrial Control Systems Cyber Emergency Response Team (ICS-CERT) investigation covers a wide range of devices, but most, if not all, devices are capable of connecting to an IT network, which dramatically increases the devices’ susceptibility to hacking.
Threats and Vulnerabilities
There is a gamut of cybersecurity vulnerabilities that can impact medical devices and hospital network operations. One of the major problems is the use of off-the-shelf software (OTS) in medical devices. About 50% of devices on a hospital network use Windows and 30-40% use Linux or Unix. A cybersecurity vulnerability exists whenever the OTS software provides an opportunity for unauthorized access to the network or the medical device. Cybersecurity vulnerabilities open the door to unwanted software changes that may impact the safety and effectiveness of the medical device.
The overriding issue is the product lifetime mismatch. While software operating systems typically last only a few years before being replaced by a new version, the lifetime of a medical device can often stretch to 15-20 years. Due to this, existing devices often run on defunct operating systems, or systems that have not been patched according to the manufacturer’s recommendation, making them susceptible to hackers.
Additional vulnerabilities center around password management. Newer devices could have built-in “Admin” passwords that are hard to change and available through a Google search. Initial passwords are often intentionally disabled to provide hospital staff an easier access but also inadvertently making access easier for the hacker. A common technique is to use a medical device as a “pivot point”, gaining network access through the unprotected device, and pivoting toward the heart of the network and the valuable patient records. Hackers have also emailed hospital employees malicious code, or malware, which, when opened, could make its way through the network to medical devices and jeopardize the devices.
These vulnerabilities are now spread out across an increasing number of devices connected to the hospital network and often directly to the internet, making the challenge to control the problem even more complex.
Security Drivers for Medical Device Manufacturers
The Customer
In light of the cybersecurity developments, many hospitals began requiring that MDMs provide evidence that their devices are securable and not susceptible to cybersecurity threats. When a data breach occurs, hospitals are faced with lawsuits, resulting in financial loss, damage to their reputations and increased insurance rates. HDOs now realize their liability exposure and have every intention of getting vendors to help mitigate the risk. For example, Mayo Clinic now requires that device security be validated before purchase. The requirements include a vulnerability assessment, fuzz testing and pen testing, along with documented evidence of testing.
By having this information available to the customer at the pre-purchase stage, the MDM can gain an advantage over competitors when the device features are otherwise similar. In fact, these tests need to be performed throughout the device development cycle to eliminate surprises at the end of the process.
Regulatory Demands: U.S. Food and Drug Administration
The FDA’s draft cybersecurity guidance was first published in June 2013, with the final edition, “Content of Premarket Submissions for Management of Cybersecurity in Medical Devices”, following in October 2014. The guideline calls on MDMs to take security into account during the device design and development phase and to consider cybersecurity risks as part of the required risk analysis. The emphasis of the guideline is on the device functionality and patient safety, rather than data protection.
Although the FDA guidelines themselves are not legally binding, they represent the FDA’s view, or interpretation, of the regulations and are likely to become mandatory down the road. Therefore, manufacturers can expect the FDA to request evidence that the guideline is followed when submitting the 510(k) documentation for clearance or a Premarket Approval Application (PMA) for approval.
The cybersecurity guideline scope is very broad and applicable to all premarket submissions for medical devices containing software, programmable logic, and standalone software that is considered a medical device. Special attention is paid to networked devices.
General Principles of the FDA Cybersecurity Guidance
The FDA recognizes that medical device security is a shared responsibility among stakeholders, including HDOs, patients, and MDMs. The organization wants to see a partnership between MDMs and HDOs to assure cybersecurity.
MDMs’ role is to develop a set of cyber controls to secure a medical device and maintain its functionality and safety. They are advised to establish a cybersecurity vulnerability and management approach as part of the software validation and risk analysis that is required by Code of Federal Regulations Title 21 Section 820.30(g).
When establishing cybersecurity design inputs, MDMs should address the following elements:
Expanding the Risk Analysis
Today’s interconnected world broadens the application of risk analysis for MDMs. Risk analysis must consider the device security in the face of malicious malware and criminal hackers whose primary intent is to use the device as an entry point to the network. In addition, hackers can obtain valuable patient records and potentially inflict harm to patients or hospital medical devices.
The FDA regulates safety in devices; the Department of Homeland Security and HDOs look for security; and the HIPAA mandates patient privacy. Threats and vulnerabilities related to all three areas have to be considered in the risk analysis.
When assessing the impact on safety, privacy and security, MDMs need to consider both patient safety/loss of device availability and the likelihood of the device becoming susceptible to a data breach. Then, they need to determine the likelihood of a threat event and harm or impact of adverse effects to the patient, hospital and device maker’s reputation.
The FDA’s Suggested Documentation
The FDA is looking for manufacturers to provide a narrative describing how the devices’ security profile fits the intended use and environment of the device. In their cybersecurity risk management approach, MDMs should document the following:
Evaluate both intentional and unintentional cybersecurity risks:
Why TÜV Rheinland?
TÜV Rheinland, a 143-year-old global testing and certification organization, and OpenSky Corporation, a leading provider of information technology (IT) consulting services and now a division of TÜV Rheinland, pulled their expertise together to introduce a unique portfolio of services to MDMs and HDOs, including assessment, testing and remediation services. The program is designed to meet both the market and regulatory requirements.
The company’s security analysts determine possible technical threats to the IT systems, infrastructure, or applications used within the organization. In doing so, experts use the same strategies and tools as actual hackers, although for a different end. Their aim is to uncover vulnerabilities and loopholes and close them before an actual hacker discovers them.
TÜV Rheinland offers a wide range of cybersecurity related services, including:
The other side of the coin, however, is that these networks are more susceptible to hacking to gain access to the main hospital network, steal sensitive patient information, and, possibly, cause devices to malfunction, leading to patient harm. Hackers often exploit vulnerabilities within a medical device software or security loopholes within the wider network to access and steal medical records. From August 2009 to December 2013, 804 major breaches occurred at healthcare delivery organizations (HDO), with “major” defined as more than 500 patient records. (United States Department of Health and Human Services.)
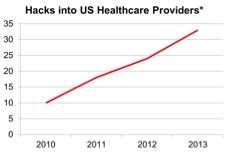
(Source: www.privacyrights.org) *Publicly known
The issue has figured prominently in the minds of the public and all industry players. In October 2014, the U.S. Department of Homeland Security (DHS) announced it is investigating about two dozen cases of suspected cybersecurity flaws in medical devices and hospital equipment that officials fear could be exploited by hackers.
The DHS’s Industrial Control Systems Cyber Emergency Response Team (ICS-CERT) investigation covers a wide range of devices, but most, if not all, devices are capable of connecting to an IT network, which dramatically increases the devices’ susceptibility to hacking.
Threats and Vulnerabilities
There is a gamut of cybersecurity vulnerabilities that can impact medical devices and hospital network operations. One of the major problems is the use of off-the-shelf software (OTS) in medical devices. About 50% of devices on a hospital network use Windows and 30-40% use Linux or Unix. A cybersecurity vulnerability exists whenever the OTS software provides an opportunity for unauthorized access to the network or the medical device. Cybersecurity vulnerabilities open the door to unwanted software changes that may impact the safety and effectiveness of the medical device.
The overriding issue is the product lifetime mismatch. While software operating systems typically last only a few years before being replaced by a new version, the lifetime of a medical device can often stretch to 15-20 years. Due to this, existing devices often run on defunct operating systems, or systems that have not been patched according to the manufacturer’s recommendation, making them susceptible to hackers.
Additional vulnerabilities center around password management. Newer devices could have built-in “Admin” passwords that are hard to change and available through a Google search. Initial passwords are often intentionally disabled to provide hospital staff an easier access but also inadvertently making access easier for the hacker. A common technique is to use a medical device as a “pivot point”, gaining network access through the unprotected device, and pivoting toward the heart of the network and the valuable patient records. Hackers have also emailed hospital employees malicious code, or malware, which, when opened, could make its way through the network to medical devices and jeopardize the devices.
These vulnerabilities are now spread out across an increasing number of devices connected to the hospital network and often directly to the internet, making the challenge to control the problem even more complex.
Security Drivers for Medical Device Manufacturers
The Customer
In light of the cybersecurity developments, many hospitals began requiring that MDMs provide evidence that their devices are securable and not susceptible to cybersecurity threats. When a data breach occurs, hospitals are faced with lawsuits, resulting in financial loss, damage to their reputations and increased insurance rates. HDOs now realize their liability exposure and have every intention of getting vendors to help mitigate the risk. For example, Mayo Clinic now requires that device security be validated before purchase. The requirements include a vulnerability assessment, fuzz testing and pen testing, along with documented evidence of testing.
By having this information available to the customer at the pre-purchase stage, the MDM can gain an advantage over competitors when the device features are otherwise similar. In fact, these tests need to be performed throughout the device development cycle to eliminate surprises at the end of the process.
Regulatory Demands: U.S. Food and Drug Administration
The FDA’s draft cybersecurity guidance was first published in June 2013, with the final edition, “Content of Premarket Submissions for Management of Cybersecurity in Medical Devices”, following in October 2014. The guideline calls on MDMs to take security into account during the device design and development phase and to consider cybersecurity risks as part of the required risk analysis. The emphasis of the guideline is on the device functionality and patient safety, rather than data protection.
Although the FDA guidelines themselves are not legally binding, they represent the FDA’s view, or interpretation, of the regulations and are likely to become mandatory down the road. Therefore, manufacturers can expect the FDA to request evidence that the guideline is followed when submitting the 510(k) documentation for clearance or a Premarket Approval Application (PMA) for approval.
The cybersecurity guideline scope is very broad and applicable to all premarket submissions for medical devices containing software, programmable logic, and standalone software that is considered a medical device. Special attention is paid to networked devices.
General Principles of the FDA Cybersecurity Guidance
The FDA recognizes that medical device security is a shared responsibility among stakeholders, including HDOs, patients, and MDMs. The organization wants to see a partnership between MDMs and HDOs to assure cybersecurity.
MDMs’ role is to develop a set of cyber controls to secure a medical device and maintain its functionality and safety. They are advised to establish a cybersecurity vulnerability and management approach as part of the software validation and risk analysis that is required by Code of Federal Regulations Title 21 Section 820.30(g).
When establishing cybersecurity design inputs, MDMs should address the following elements:
- Identification of assets, threats, and vulnerabilities;
- Assessment of the impact of threats and vulnerabilities on device functionality, end users and patients;
- Assessment of the likelihood of a threat and of a vulnerability being exploited;
- Determination of risk levels and suitable mitigation strategies; and
- Assessment of residual risk and risk acceptance criteria.
Expanding the Risk Analysis
Today’s interconnected world broadens the application of risk analysis for MDMs. Risk analysis must consider the device security in the face of malicious malware and criminal hackers whose primary intent is to use the device as an entry point to the network. In addition, hackers can obtain valuable patient records and potentially inflict harm to patients or hospital medical devices.
The FDA regulates safety in devices; the Department of Homeland Security and HDOs look for security; and the HIPAA mandates patient privacy. Threats and vulnerabilities related to all three areas have to be considered in the risk analysis.
When assessing the impact on safety, privacy and security, MDMs need to consider both patient safety/loss of device availability and the likelihood of the device becoming susceptible to a data breach. Then, they need to determine the likelihood of a threat event and harm or impact of adverse effects to the patient, hospital and device maker’s reputation.
The FDA’s Suggested Documentation
The FDA is looking for manufacturers to provide a narrative describing how the devices’ security profile fits the intended use and environment of the device. In their cybersecurity risk management approach, MDMs should document the following:
Evaluate both intentional and unintentional cybersecurity risks:
- Provide information on the threats considered and risks analyzed and
- Make use of MITRE’s Common Vulnerabilities and Exploits (CVE).
- Establish controls to mitigate risk:
- Provide information on the controls put in place and
- Provide information on the appropriateness of the controls to mitigate identified risk.
- Create a matrix linking cybersecurity controls to the current threats and risks being mitigated. Ideally, the matrix should be linked to the CVE’s.
- Provide a summary describing the plan and controls to assure the device does the following:
- Leaves the manufacturer malware-free,
- Software maintains integrity throughout lifecycle through validated patches and updates, and
- Instructions for use related to recommended cybersecurity controls are appropriate for the intended use environment.
Why TÜV Rheinland?
TÜV Rheinland, a 143-year-old global testing and certification organization, and OpenSky Corporation, a leading provider of information technology (IT) consulting services and now a division of TÜV Rheinland, pulled their expertise together to introduce a unique portfolio of services to MDMs and HDOs, including assessment, testing and remediation services. The program is designed to meet both the market and regulatory requirements.
The company’s security analysts determine possible technical threats to the IT systems, infrastructure, or applications used within the organization. In doing so, experts use the same strategies and tools as actual hackers, although for a different end. Their aim is to uncover vulnerabilities and loopholes and close them before an actual hacker discovers them.
TÜV Rheinland offers a wide range of cybersecurity related services, including:
- Security management program and framework development,
- Privacy and security-focused risk assessments,
- Attack analysis based on device characteristics and operating environment,
- Dynamic vulnerability assessment and penetration testing,
- Fuzz testing,
- Secure SDLC integration,
- Static code security testing,
- Mobile application security testing,
- Plan development for dealing with existing/legacy devices, and
- Full consulting support to fulfill the FDA’s cybersecurity guidance, i.e. writing the “narrative,” preparing the matrix, lifecycle plan and instructions for use.