Kevin von Keyserling, Chief Strategy Officer at Keyfactor09.17.19
Between staffing, general administration and operational expenditures, the cost of serving a patient end-to-end is astronomical. As value-based care becomes more prevalent, healthcare delivery organizations (HDOs) are looking to transform this model with goals of reducing costs, optimizing patient outcomes and driving better financial performance.
A core component of this transformation is the shift to telemedicine or virtual healthcare. Advances in medical technology, combined with the power of digital connectivity, is allowing the doctor/patient interaction within a perioperative environment to become a partnership. While these momentous changes are breaking down healthcare administration and delivery barriers, digital security is becoming an even more important component of this evolving ecosystem. Those within the perioperative cycle must be confident that every input, action, and device that’s incorporated into the patient health plan is digitally secure.
The Internet of Medical Things
The Internet of Medical Things (IoMT) interconnects devices through data exchanges, enabling machine-to-machine interaction and real-time data streaming. When equipped with sensors, IoMT devices can vary from prostheses and implantable medical devices (e.g. pacemakers) to medical equipment (e.g. stretchers) and home-use medical devices (e.g. blood pressure cuffs). Due to growing demand, experts predict that there will be between 20 and 30 billion devices within the IoMT by 2020.
Three types of medical devices easily align with this new shift of collaborative HDO/virtual patient care:
Building Trust While Innovating
Given the growth of connected medical devices, the potential for security lapses from release through use is considerable. While implanted devices draw the most attention, the broader universe of medical care gadgets can also warrant concern. In the U.S. alone, hospitals can average anywhere between 10 to 15 connected devices per-bed. With this kind of scale, the number of security gaps can be significant.
Medical devices that feature wireless connectivity, remote monitoring, and near-field communication technology allow health professionals to adjust and fine tune implanted devices remotely and in real-time. Devices capture and transmit data across many channels and receiving parties, but many fail to incorporate data security protocols and standards. Older devices that remain in the field may be using outdated security software. There is also significant ambiguity on who owns the data, which can result in nobody taking the lead on managing current security practices.
Put these factors together and it’s easy to understand why healthcare data is highly susceptible to security failures. Cyberattacks can be initiated by external bad actors, internal staff who make mistakes, or a lax digital security implementation. Additionally, guidelines from the FDA are not mandated, and with a lack of funding and resources, comprehensive security reports may be overlooked to achieve other organizational priorities.
Protecting Patient Privacy: It’s All about the Data
There’s a treasure trove of information captured and stored in healthcare and the prize money from insurance fraud and black-market pharmaceutical sales can be extremely lucrative. Healthcare has the highest breach-related costs of any industry at $408 per-stolen record. As patients willingly share personally identifiable information (PII), often over open networks, reliable controls must be in place to protect patient privacy. Think of your organization as an entity with identities. These identities are made up of people, applications, and devices. Every identity has a role to play in the exchange of data. To create a secure environment for these data exchanges, every identity within the organization must be covered by layers of digital security. Knowing where you are and where you want to go can be overwhelming, but breaking the process down into smaller bites can help ensure you’re setting the stage for optimized data and device security without taking everything on all at once.
Here are a few ways to get started:
Kevin von Keyserling is chief strategy officer at Keyfactor, a leading provider of secure digital identity management solutions. In this role, von Keyserling is responsible for company operations and oversees Keyfactor’s organic and acquisition growth strategy. For more information visit: www.keyfactor.com or follow @Keyfactor on Twitter and LinkedIn.
A core component of this transformation is the shift to telemedicine or virtual healthcare. Advances in medical technology, combined with the power of digital connectivity, is allowing the doctor/patient interaction within a perioperative environment to become a partnership. While these momentous changes are breaking down healthcare administration and delivery barriers, digital security is becoming an even more important component of this evolving ecosystem. Those within the perioperative cycle must be confident that every input, action, and device that’s incorporated into the patient health plan is digitally secure.
The Internet of Medical Things
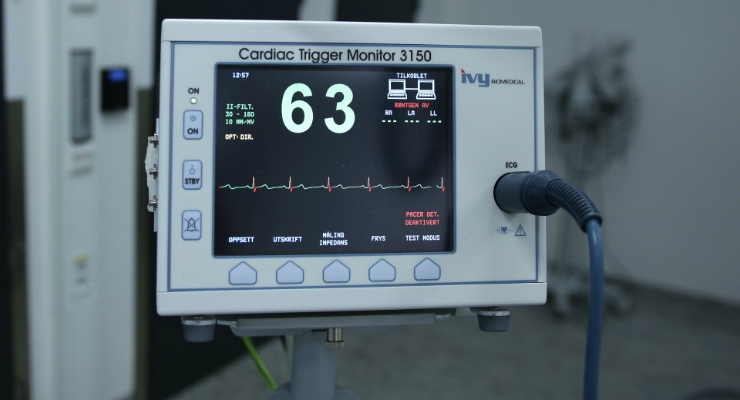
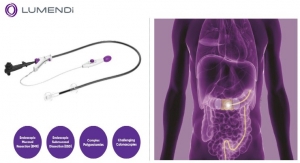
The Internet of Medical Things (IoMT) interconnects devices through data exchanges, enabling machine-to-machine interaction and real-time data streaming. When equipped with sensors, IoMT devices can vary from prostheses and implantable medical devices (e.g. pacemakers) to medical equipment (e.g. stretchers) and home-use medical devices (e.g. blood pressure cuffs). Due to growing demand, experts predict that there will be between 20 and 30 billion devices within the IoMT by 2020.
Three types of medical devices easily align with this new shift of collaborative HDO/virtual patient care:
- Wearable External Devices: incorporate biosensors to monitor patient data via remote/wireless communication, which can be used for telemedicine and patient monitoring of blood pressure, EKG, temperature, glucose levels, oxygen levels, etc.
- Implantable Medical Devices (IMDs): may replace a missing biological structure, support a damaged biological structure, or enhance an existing biological structure (e.g. implantable infusion pumps and other drug-delivery devices, cardiac pacemakers, implantable neuro-stimulator systems and glucose monitors).
- Stationary Medical Devices: a wide range of stationary medical equipment, used for various applications like clinical operations (surgical devices) and connected imaging (x-ray and MRI machines), lab tests, patient monitoring, drug delivery, medication management, etc.
Building Trust While Innovating
Given the growth of connected medical devices, the potential for security lapses from release through use is considerable. While implanted devices draw the most attention, the broader universe of medical care gadgets can also warrant concern. In the U.S. alone, hospitals can average anywhere between 10 to 15 connected devices per-bed. With this kind of scale, the number of security gaps can be significant.
Medical devices that feature wireless connectivity, remote monitoring, and near-field communication technology allow health professionals to adjust and fine tune implanted devices remotely and in real-time. Devices capture and transmit data across many channels and receiving parties, but many fail to incorporate data security protocols and standards. Older devices that remain in the field may be using outdated security software. There is also significant ambiguity on who owns the data, which can result in nobody taking the lead on managing current security practices.
Put these factors together and it’s easy to understand why healthcare data is highly susceptible to security failures. Cyberattacks can be initiated by external bad actors, internal staff who make mistakes, or a lax digital security implementation. Additionally, guidelines from the FDA are not mandated, and with a lack of funding and resources, comprehensive security reports may be overlooked to achieve other organizational priorities.
Protecting Patient Privacy: It’s All about the Data
There’s a treasure trove of information captured and stored in healthcare and the prize money from insurance fraud and black-market pharmaceutical sales can be extremely lucrative. Healthcare has the highest breach-related costs of any industry at $408 per-stolen record. As patients willingly share personally identifiable information (PII), often over open networks, reliable controls must be in place to protect patient privacy. Think of your organization as an entity with identities. These identities are made up of people, applications, and devices. Every identity has a role to play in the exchange of data. To create a secure environment for these data exchanges, every identity within the organization must be covered by layers of digital security. Knowing where you are and where you want to go can be overwhelming, but breaking the process down into smaller bites can help ensure you’re setting the stage for optimized data and device security without taking everything on all at once.
Here are a few ways to get started:
- Improve the strength of targeted devices: Establish necessary barriers between the device and an outside threat. Utilize features such as auto-lock when a device, such as a cell phone or laptop, leaves a certain area or space. It all comes down to understanding what materials have gone into the construction of the device. Are these materials permeable or easy to manipulate?
- Control access: How do you want to define your security protocol? Can the devices being used be patched? Make sure you have a regular cadence in which passwords need to be updated and utilize multi-factor authentication when possible.
- On-site security: Be aware of your device inventory always – no device should ever be left unattended! Ensure that all devices are locked in a restricted and secure area when not in use.
- Encrypt, encode: Encryption is “Digital Security 101” and used to keep the bad guys out of good data. That, along with authentication and authorization are the lifeblood of success digital identity security. Having unique digital certificates that cover every identity validate that a device is authentic and assert with high assurance that its messages are genuine.
- Know your partners and suppliers: Make sure any vendors and/or OEMs that you work with are vetted. Don’t be afraid to have an open dialogue with your vendor about their attention to security – they should place as much importance on it as you do.
- Invest in digital security automation: Manual processes are prone to errors. Automation drives high assurance that every investment you’ve made in building your digital security program will work. Workflows become refined and execution gets easier.
- Follow industry guidelines and standards: By following recommended standards, you’ll reduce risk both inside and outside your organization. Regular cadences and audits on log files, pending digital certificate expirations, personnel changes and regulatory updates help detect issues and can provide the runway you need to prevent catastrophe.
- Build a team: Creating shared responsibility in protecting patients by building a flexible, collaborative team provides the opportunity to have ongoing, two-way dialogue and input regarding security.
- Consider a technology vendor for help: No matter how you’re delivering healthcare today, security must be top of mind for both current processes and future innovations. Don’t let the enormity of the mission result in in-action. Identifying the right partner can help you determine how best to invest in the right technologies. Many vendors have a broad portfolio of enterprise and IoT security solutions specifically designed for the healthcare segment, with proven platforms and expanding capabilities designed for HDOs, EHRs and OEMs alike.
Kevin von Keyserling is chief strategy officer at Keyfactor, a leading provider of secure digital identity management solutions. In this role, von Keyserling is responsible for company operations and oversees Keyfactor’s organic and acquisition growth strategy. For more information visit: www.keyfactor.com or follow @Keyfactor on Twitter and LinkedIn.