David West, Director of Professional Services, Icon Labs08.05.16
Reports of insecure medical devices have consistently made headlines in the past several years. The FDA and Department of Homeland Security issued an alert urging medical device makers and medical facilities to immediately upgrade system security and procedures to protect against potential cyber threats. This alert came in response to an ICS-CERT publication listing more than 300 devices with hard-coded passwords. Hacked medical devices have been used to steal patient records, including insurance information, and have been shown to be vulnerable to a wide range of attacks.
Hard-coded passwords are a huge and unacceptable security loophole because it makes it quite easy for hackers to successfully guess or discover the passwords. Also, in many cases, hard-coded passwords are available in the device’s operating manuals and FAQs and shared among the hacking community. Even worse, the use of hard-coded passwords means that there is no way for the end user or facility to change the password to improve security.
Upgrading medical devices to require a complex password is a quick and important fix that should be done as soon as possible. While helpful to prevent some low-level attacks, it still falls far short of providing the type of security truly required to reliably protect against today’s cyber threat environment.
What Security Requirements Do Medical Devices Really Need?
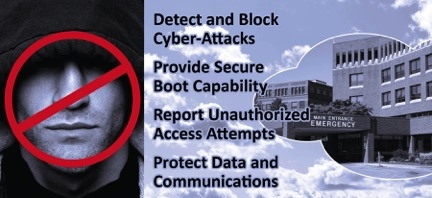
A security solution for medical devices must provide the ability to control communications, detect and report attacks or suspicious traffic patterns, and allow centralized control of security policies. These capabilities provide medical devices with a much higher level of security than password-only security and protect them from the majority of cyber attacks.
The security solution must provide:
As shown in the ICS-CERT report, many legacy medical devices and systems used in medical facilities worldwide were manufactured with inadequate security. Upgrading these devices to improve security requires the device manufacturer to develop a newer software or firmware version with improved security. Once the new version is available, the devices can be upgraded to provide enhanced security.

The Icon Labs Floodgate Defender appliance is easy to install and provides a cost effective “bump in the wire” solution to protect existing medical equipment and systems.
Unfortunately, the upgrade process may be difficult and expensive. Some devices cannot be upgraded without being returned to the factory. In some instances, the manufacturer may no longer support the device, or may be out of business. Replacing these devices is often simply too expensive to be an option and newer devices may not yet be available with improved security.
For medical equipment and systems not easily or affordably replaced or upgraded, an inline firewall appliance provides missing security. It protects legacy devices by creating a secure enclave where only trusted devices can operate. These devices can freely communicate with each other; however, communication outside the enclave is controlled for security. The appliance provides security by enforcing communication policies, ensuring only valid communication is allowed with the endpoints within the secure enclave.
By limiting communication to the secure enclave, the appliance:
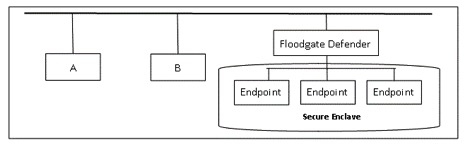
The Floodgate Defender is located between endpoint devices to be protected and the internet or company network.
Securing New Devices: The Integrated Solution
For new devices, enhanced security can be built into the device itself. This is the same approach taken with PCs today. While a PC may sit behind a firewall on a protected home or corporate network, it also has a built-in firewall and other security software.
Building protection into the device itself provides another security layer. The devices are no longer depending on the corporate firewall as their sole layer of security. An integrated firewall provides a basic, but critical level of security for a networked device by controlling which packets are processed by the device. The embedded firewall resides inside the device and integrates into the communication stack of the device. The communication requirements of the device are encoded into a set of policies defining allowable communication. The built-in firewall enforces these polices, limiting communication to just the approved, required IP addresses, ports, and protocols.
Since each packet or message received by the device is filtered by the firewall before being passed from the protocol stack to the application, many attacks are blocked before a connection is even established, thereby providing a simple, yet effective layer of protection missing from most medical devices.
Blocking Attacks with a Firewall
In a system without a firewall, a hacker may attempt to remotely access the device using default passwords, dictionary attacks, or stolen passwords. Such attacks are often automated, allowing a huge number of attempts to break the system’s password. By protecting the system with an embedded firewall configured with a whitelist of trusted hosts, attacks are effectively blocked. The firewall blocks packets from the hacker before the packet is passed to the application to attempt to login.
Rules-based filtering provides a simple and effective tool to enforce communication policies, blocking communication from a non-trusted IP address and isolating the device from attack. The firewall’s intrusion detection alerts system administrators to unusual activities about malicious network traffic…think of it as a security camera for the network.
Conclusion
Many of today’s modern medical devices and systems are complex connected embedded computers charged with performing critical functions. Firewalls provide the cornerstone of security both for PCs and for home or corporate networks. Including a firewall in new medical devices themselves, or by placing several devices within a secure enclave, provides a simple and effective layer of security. These firewalls provide protection even if the corporate firewall and security have been breached. A small, embedded firewall can be used to protect devices from a wide range of cyber attacks. By controlling who the device talks to, most attacks can be blocked before a connection is even established.
David West is the director of professional services at Icon Labs, a leading provider of security solutions for embedded devices. You can reach him at david.west@iconlabs.com.
Hard-coded passwords are a huge and unacceptable security loophole because it makes it quite easy for hackers to successfully guess or discover the passwords. Also, in many cases, hard-coded passwords are available in the device’s operating manuals and FAQs and shared among the hacking community. Even worse, the use of hard-coded passwords means that there is no way for the end user or facility to change the password to improve security.
Upgrading medical devices to require a complex password is a quick and important fix that should be done as soon as possible. While helpful to prevent some low-level attacks, it still falls far short of providing the type of security truly required to reliably protect against today’s cyber threat environment.
What Security Requirements Do Medical Devices Really Need?
A security solution for medical devices must provide the ability to control communications, detect and report attacks or suspicious traffic patterns, and allow centralized control of security policies. These capabilities provide medical devices with a much higher level of security than password-only security and protect them from the majority of cyber attacks.
The security solution must provide:
- Complete control of the packets processed by the device
- Protection from hackers and cyber attacks that may be launched from the internet, inside the clinical network (frequently launched by trusted employees), or from “trusted” vendors (i.e., the Target attack)
- Protection from Denial of Service attacks and packet floods
- Ability to detect, block, and report traffic abnormalities, probes, or attacks
- Ability to manage and control changes to filtering policies
As shown in the ICS-CERT report, many legacy medical devices and systems used in medical facilities worldwide were manufactured with inadequate security. Upgrading these devices to improve security requires the device manufacturer to develop a newer software or firmware version with improved security. Once the new version is available, the devices can be upgraded to provide enhanced security.

The Icon Labs Floodgate Defender appliance is easy to install and provides a cost effective “bump in the wire” solution to protect existing medical equipment and systems.
For medical equipment and systems not easily or affordably replaced or upgraded, an inline firewall appliance provides missing security. It protects legacy devices by creating a secure enclave where only trusted devices can operate. These devices can freely communicate with each other; however, communication outside the enclave is controlled for security. The appliance provides security by enforcing communication policies, ensuring only valid communication is allowed with the endpoints within the secure enclave.
By limiting communication to the secure enclave, the appliance:
- Prevents probes and hacking drones from discovering endpoints. Hackers and automated drones send out ping requests or other messages to a range of IP addresses looking for responses. The security appliance drops these requests, making the endpoints undiscoverable.
- Prevents access from unauthorized machines. Many specialized medical devices only need to communicate with a few known, trusted host computers. Enforcing these communication restrictions prevents communication with unauthorized machines. If a hacker cannot communicate with the endpoint, they cannot compromise it.
- Close security loopholes. Many cyber attacks utilize services on an endpoint not required for fixed function devices. Blocking unused ports and protocols closes these commonly exploited security loopholes.
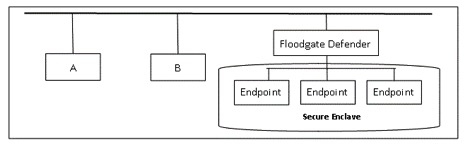
The Floodgate Defender is located between endpoint devices to be protected and the internet or company network.
Securing New Devices: The Integrated Solution
For new devices, enhanced security can be built into the device itself. This is the same approach taken with PCs today. While a PC may sit behind a firewall on a protected home or corporate network, it also has a built-in firewall and other security software.
Building protection into the device itself provides another security layer. The devices are no longer depending on the corporate firewall as their sole layer of security. An integrated firewall provides a basic, but critical level of security for a networked device by controlling which packets are processed by the device. The embedded firewall resides inside the device and integrates into the communication stack of the device. The communication requirements of the device are encoded into a set of policies defining allowable communication. The built-in firewall enforces these polices, limiting communication to just the approved, required IP addresses, ports, and protocols.
Since each packet or message received by the device is filtered by the firewall before being passed from the protocol stack to the application, many attacks are blocked before a connection is even established, thereby providing a simple, yet effective layer of protection missing from most medical devices.
Blocking Attacks with a Firewall
In a system without a firewall, a hacker may attempt to remotely access the device using default passwords, dictionary attacks, or stolen passwords. Such attacks are often automated, allowing a huge number of attempts to break the system’s password. By protecting the system with an embedded firewall configured with a whitelist of trusted hosts, attacks are effectively blocked. The firewall blocks packets from the hacker before the packet is passed to the application to attempt to login.
Rules-based filtering provides a simple and effective tool to enforce communication policies, blocking communication from a non-trusted IP address and isolating the device from attack. The firewall’s intrusion detection alerts system administrators to unusual activities about malicious network traffic…think of it as a security camera for the network.
Conclusion
Many of today’s modern medical devices and systems are complex connected embedded computers charged with performing critical functions. Firewalls provide the cornerstone of security both for PCs and for home or corporate networks. Including a firewall in new medical devices themselves, or by placing several devices within a secure enclave, provides a simple and effective layer of security. These firewalls provide protection even if the corporate firewall and security have been breached. A small, embedded firewall can be used to protect devices from a wide range of cyber attacks. By controlling who the device talks to, most attacks can be blocked before a connection is even established.
David West is the director of professional services at Icon Labs, a leading provider of security solutions for embedded devices. You can reach him at david.west@iconlabs.com.